Updated April 22, 2024
When we think of cyber threats, we often think of the dark web, criminal hacking gangs, and external forces breaching a network. It’s a big misconception as cybersecurity experts know some of the riskiest threats are inside your organization. And these insider threats are on the rise. It’s been reported that the frequency of insider-led incidents was up as much as 44% in 2022.
There are a variety of societal factors impacting the rise in insider attacks. Some employees are disgruntled about return-to-work policies, the labor force is changing jobs more often, we’ve seen massive layoffs in the tech industry, there is looming economic uncertainty, and cybercrime recruitment efforts are on the rise. The 2023 Insider Threat Report from Cybersecurity Insiders found that 74% of organizations say insider attacks have become more frequent and 74% of organizations also felt they are at least moderately vulnerable or worse to insider threats.
We will take a closer look at who is an insider, common insider threat indicators, and some tips for minimizing your risk of an insider attack.
What is an insider threat?
An insider threat is the potential for an insider in your organization to use their authorized access or special knowledge to harm your organization. It’s a security breach caused by someone with inside access to the company.
Who is an insider?
That begs the question – who exactly is an insider? The Cybersecurity & Infrastructure Security Agency (CISA) defines an insider as any person who currently has or previously had authorized access to knowledge of an organization’s resources. The resources include personnel, facilities, information, equipment, networks, and systems. Insiders can be broken down into three groups.
- Regular employees. These employees have limited capabilities but can still harm an organization. For instance, they can misuse company data, install unauthorized applications, send confidential emails to the wrong address, or become the victim of a phishing attack.
- Privileged users. These users are administrators, C-level executives, and others with a higher level of access privileges. They have access to your organization’s critical infrastructure and sensitive data, so they can cause significant damage as an insider threat.
- Third parties. This group includes vendors, subcontractors, and business partners that have access to your IT systems or data. Third parties may not follow your established cybersecurity rules or could violate them maliciously. Hackers can also gain access through a poorly secured third-party vendor to get inside your company’s perimeter.
Types of insider threats
Within those groups of insiders, there were various types of threats mentioned. Generally, insider threats can be broken into two primary kinds of activity – unintentional and intentional.
- Unintentional. Insiders can expose an organization unintentionally through negligence or a mistake. Negligence involves an insider having a basic understanding of security and IT policies, but the insider doesn’t consider them a priority and ignores them. A mistake is just as it sounds – accidentally or inadvertently sending or clicking on something that causes a threat to the company.
- Intentional. There are also insiders who may intentionally and maliciously take actions to harm an organization for personal benefit or because of a personal grievance. Malicious insider threats may involve a disgruntled employee, someone under extreme financial pressure, an associate trying to advance their career through stolen intellectual property, or an employee who feels they were unfairly terminated and is seeking revenge.
Common malicious insider threat indicators
Mistakes can happen, but it’s important to know what to look for when it comes to intentional insider threats. Let’s take a closer look at some common indicators of an insider threat.
- Unusual behavior: Any sudden change in behavior, such as increased secrecy, unusual working hours, or unexplained absences, can be a sign of potential insider threat.
- Accessing unauthorized information: Employees accessing files or systems they don't typically use, especially if it involves sensitive or confidential information, may indicate malicious intent.
- Data exfiltration: Suspicious activities involving the transfer or copying of sensitive data, particularly if it occurs outside of regular business hours or involves unusual destinations, could signal insider threats.
- Disgruntled employees: Individuals who express dissatisfaction with their job, colleagues, or the organization itself may pose a higher risk of insider threats, especially if they have access to critical systems or data.
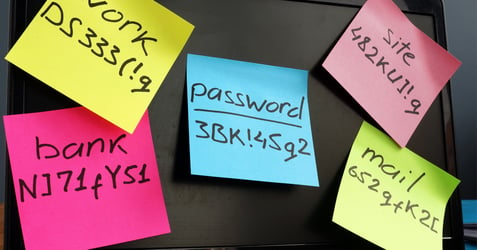
- Misconduct and policy violations: Instances where employees disregard or bypass security protocols, such as sharing passwords, disabling security measures, or accessing restricted areas, could be red flags. Past incidents of policy violations, disciplinary actions, or conflicts with colleagues may indicate a propensity for unethical or malicious behavior.
Seven tips to mitigate insider threats
Because there are so many risks, both malicious and accidental, there is no one magic bullet to prevent an insider from wreaking havoc on your organization. Instead, there are some tips and best practices for your company to consider for reducing the risk of both intentional and unintentional insider threats.
- Hiring and personnel management. Besides strong vetting in your hiring practices, you should also be on the lookout for red flags during performance reviews. Indicators to watch for include disgruntled employees and those who indicate significant financial changes. Using credit checks upon hire can also help indicate candidates with high levels of debt that could be tempted to act for financial gain. In addition, employees who receive special access to sensitive resources should undergo a background check.
- Establish a protective and supportive culture. A protective culture gives employees confidence that preventing insider attacks is supportive of their company goals and values. Organizations should establish a climate of accountability, respect, and collective responsibility. In this type of culture, employees are enabled to speak openly about concerns with the confidence leadership will act on them while also protecting employees’ privacy.
- Security education awareness and training. Cybersecurity awareness training empowers employees to recognize and avoid common threats through ongoing training. Employees are tested on common threat tactics like social engineering, phishing, spoofing, and ransomware to help reduce unintentional insider threats. Because the cyber security landscape is evolving, there should be ongoing training occurring throughout the year – it’s not just one and done.
- Multifactor authentication. Enabling multifactor authentication (MFA) to enhance identity and access management is a strong security measure to consider. It requires two or more verification factors to check user identity before someone gains access to the network. Having MFA in place means an employee can’t simply share a login or password with someone outside your organization and allow them to gain access.
- Lockdown permissions on collaboration platforms. While establishing an intranet, share point, and Microsoft Teams portal can improve the ability of your employees to collaborate, it also poses risks. Review the lockdown permission levels in these systems to ensure your employees can access them while also securing application pages.
- Employee separation. All system access should be revoked immediately when an employee leaves. In addition, you may want to consider forgoing the usual two-week notice period once notice is given, so access can be removed immediately. This is especially true if the employee has a history of misconduct or policy violations.
- Establish identity policies. Many organizations now are establishing clear identity and access management policies. These policies establish guidelines for how identities should be authenticated, how authorizations should be managed, and how privileges and access should be deprovisioned upon separation or a change in role.
The consequences of an insider incident can ripple through an organization with devastating outcomes and long-term negative impacts. As the cybersecurity landscape becomes more complex and economic pressures continue to strain the labor market, it’s important to stay aware of insider threat trends to create a positive strategy that avoids unnecessary risks and reduces the impact on your organization.
Partner with a managed IT provider like Locknet to conduct a full security assessment of your organization and create a plan to minimize the risk of an insider threat.