Industries We Serve
World Class IT Support & Service
Real People. Right Now.
About Locknet® IT Services
From the first hello, the Locknet® team is dedicated to serving you and your needs.
Real People. Right Now.
From the first hello, the Locknet® team is dedicated to serving you and your needs.

Updated on March 30, 2026
Employees play a critical role in safeguarding company assets from cyber threats. However, they can also inadvertently expose organizations to significant risks if proper cybersecurity practices are not followed. From falling victim to sophisticated phishing attempts to using unauthorized applications, employee behaviors can create serious challenges for organizational security. As organizations adopt Zero Trust security frameworks and face increasing regulatory pressure around data protection, addressing employee cybersecurity risks has become more important than ever.
Below are nine common ways employees can introduce cybersecurity risks into the workplace. Understanding these examples can help organizations proactively address vulnerabilities and protect sensitive information.
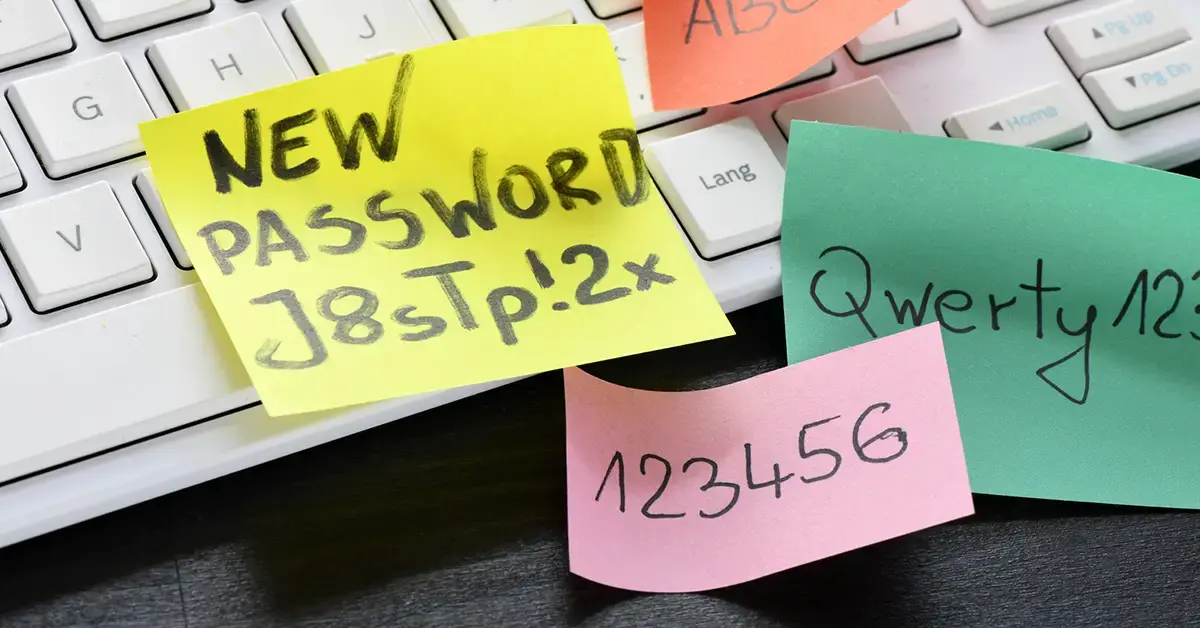
Weak Passwords
Phishing
AI Social Engineering
Public Wi-Fi
Missed Updates
Sensitive Data Mishandling
Insider Threats
BYOD Devices
Modern cybersecurity starts with identity.
Combine security awareness training with a Zero Trust framework to verify users, enforce least-privilege access, and protect organizations from employee-driven risk.
Employees are often the first line of defense against phishing attacks, yet they can also be the weakest link. Clicking on malicious links or providing sensitive information in response to deceptive emails can compromise company networks and lead to data breaches.
Today’s phishing attack examples are increasingly convincing, especially when attackers impersonate trusted brands, vendors, or internal leadership. Regular cybersecurity awareness training is essential to help employees identify suspicious emails and report potential threats before damage occurs.
Artificial intelligence has made social engineering attacks significantly more sophisticated. Attackers can now generate realistic emails, messages, voice calls, or even videos that mimic executives, vendors, or coworkers. These deepfakes and AI-powered attacks make it harder for employees to distinguish legitimate communication from malicious attempts to steal credentials or sensitive data.
Organizations should combine employee awareness training with identity-first security practices, such as multi-factor authentication (MFA), conditional access policies, and verification procedures for sensitive requests. These controls align with Zero Trust principles, where every access request must be verified regardless of its source.
Weak passwords remain one of the most common vulnerabilities exploited by cybercriminals. Employees who use easily guessable passwords or reuse credentials across multiple accounts increase the risk of unauthorized access and data breaches.
Organizations can reduce this risk by enforcing strong password cybersecurity best practices, encouraging the use of password managers, and implementing multi-factor authentication. Additionally, adopting modern authentication methods such as passkeys and biometric authentication (like fingerprint or facial recognition) can further strengthen security by reducing reliance on traditional passwords. Within a Zero Trust framework, identity becomes the primary security boundary, making strong identity protection and credential management essential for securing systems and data.
Remote and hybrid work environments have increased the likelihood that employees will access corporate resources from public networks in cafes, airports, or hotels. These unsecured Wi-Fi networks can expose sensitive data to interception by malicious actors.
Encouraging employees to use secure networks and virtual private networks (VPNs), along with implementing conditional access policies, helps ensure that sensitive resources are accessed only from trusted devices and locations.
Failing to keep software and systems up to date leaves organizations exposed to known vulnerabilities that cybercriminals actively exploit. Employees who delay installing updates or patches increase the risk of system compromise and malware infections.
Strong patch management practices, automated updates, and endpoint security policies can help organizations maintain a more resilient security posture.
Employees who mishandle sensitive information can inadvertently expose organizations to data breaches, reputational damage, and regulatory penalties. Examples include sharing confidential files through unsecured channels, storing data on personal devices, or failing to properly dispose of documents.
As data privacy regulations continue to evolve, organizations must ensure employees understand their responsibilities for protecting sensitive information. Clear data handling policies, employee training, and data loss prevention technologies can help reduce the risk of accidental exposure.
While many cybersecurity risks stem from mistakes, some originate from insiders with malicious intent. Employees, contractors, or vendors with privileged access may attempt to steal sensitive data or disrupt systems.
A Zero Trust approach can significantly reduce insider threat risks by enforcing least-privilege access, ensuring individuals only have access to the resources necessary for their role. Implementing strong identity management, monitoring privileged accounts, and enabling MFA are critical components of this strategy.
Employees sometimes adopt new tools, apps, or cloud services without approval from IT to improve productivity. This practice, known as shadow IT, can introduce serious security and compliance risks if those tools lack proper security controls.
Unauthorized applications may store sensitive data outside of approved systems, creating visibility gaps for IT teams and increasing exposure to breaches. Organizations should establish clear policies for software use and leverage identity and access controls to ensure that only approved applications connect to corporate systems.
Bring-your-own-device (BYOD) policies blur the line between personal and corporate technology. While convenient, personal devices can introduce malware or other BYOD security risks if they lack proper controls.
Organizations should implement BYOD policies that include device encryption, endpoint protection, and the ability to remotely wipe corporate data if necessary. Combining these policies with identity-based access controls and Zero Trust security models ensures that only verified users and secure devices can access company resources.
Employees can both inadvertently and intentionally expose organizations to significant cybersecurity risks. Addressing these risks requires more than awareness training alone—it also requires strong security frameworks, identity-based access controls, and technology safeguards.
By adopting Zero Trust principles, emphasizing identity-first security, and enforcing least-privilege access, organizations can significantly reduce employee-driven security risks. Combined with ongoing education and compliance-focused data protection practices, these strategies help create a more resilient security posture.
These examples are just a starting point for improving your organization’s cybersecurity readiness. Partnering with a trusted managed IT provider can help you assess vulnerabilities, implement stronger controls, and ensure your business remains protected against evolving threats.
Contact us today to learn how our managed IT services can strengthen your security, enhance productivity, and give you workplace peace of mind.
Cybersecurity

Onalaska, WI Waterloo, IA Wausau, WI Eau Claire, WI Burnsville, MN
You are now leaving locknetmanagedit.com. Please check the privacy policy of the site you are visiting.