Understanding passwordless solutions and what they can do for your business
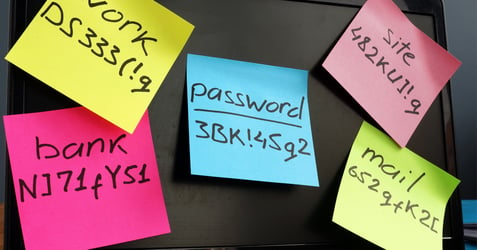
Whether you sneakily scrawl them on sticky notes, save them to your device, use an auto-generator, or somehow, miraculously remember them all, managing passwords can be a pain. (And no, we don't recommend you scrawl or save them, for security reasons). So if there were a way to do your work and manage your home accounts without them, that might simplify your life. It should come as no surprise that industry experts have developed solutions to this frequent headache, known as passwordless authentication technology.
Understanding passwordless authentication
So, what is passwordless authentication? Known by some as modern authentication, passwordless authentication uses methods other than passwords to verify a user's identity. This might include biometrics, mobile apps, or even security keys. Upon entry, users can gain secure access to the network or tools they need to use. The goals of having passwordless authentication are multifold, among them, reducing the burden on your business when it's time to log in. That means your staff spends less time struggling with passwords and more time on the task at hand. When, on average, 20-50% of all help tickets to an IT support team are password-related, solutions are often warmly welcomed. More, many passwords are vulnerable to cyberattacks, so passwordless authentication improves your ability to protect your network data.
How challenging is it to implement passwordless authentication?
Depending on the size and scope of your staff for whom you want to enable passwordless authentication, and the number of apps included as well as the complexity of your infrastructure, implementation can be a challenge. Going entirely passwordless in your user environment is unlikely, and even evolving toward partial passwordless technology won't be a quick fix, but rather, a goal that unfolds as users adopt the technology and as it becomes more sophisticated. However, given the existing burden on users and IT related to passwords and log-in difficulties, as well as the risk of stolen passwords to your network security, moving toward passwordless authentication might be a smart move for your business.
How do I start and what are some real examples of passwordless authentication in a network?
Common types of passwordless authentication include email-based, SMS-based, multi-factor, security tokens, and biometrics. Other options include piggybacking off another application, service, or device which has already authenticated the user. For example, authentication through email includes verifying a user with a link or one-time code. With a link, the user first enters their email and a unique token is created for the user and sent to them by email. Biometrics is another common form of passwordless authentication and focuses on technology such as fingerprint or face scanning. This form of authentication is commonly found on mobile devices such as laptops and smartphones. The key here is to start looking for these features start enabling them.
Reduce IT burden, boost security, and improve
user experience
Passwordless authentication can reduce security risk, lessen the burden on IT and improve user experience, so for many organizations, the choice is clear. If it's time for your business or organization to adopt passwordless authentication, the experts at Locknet Managed IT can help. Contact us to learn more about this emerging technology and how it can help your staff break free of some of the burden of passwords, and get back to business.