Updated April 14, 2024
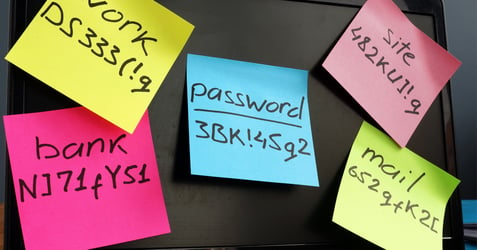
Passwords are the first line of defense against cyber threats. However, the prevalence of data breaches underscores the importance of creating strong, memorable passwords. In this blog, we'll explore the importance of creating strong, memorable passwords in the workplace and delve into strategies for crafting them effectively. Additionally, we'll fill you in on how hackers guess passwords so you can empower your employees and bolster your organization's cybersecurity posture.
The importance of strong, memorable passwords in the workplace
The ramifications of compromised passwords extend far beyond an employee’s individual accounts. A breach can lead to unauthorized access to sensitive company data, financial losses, and reputational damage. Therefore, it's imperative for employees to understand how to create strong, memorable passwords to safeguard company assets and maintain trust with clients and stakeholders.
How to create strong, memorable passwords
When creating passwords, there are some best practices to keep in mind that will give the hackers a headache and keep your information safe.
- Length and complexity: Encourage employees to use passwords with a minimum length of 12 characters, incorporating a mix of uppercase and lowercase letters, numbers, and special characters.
- Avoid common information: Avoid passwords based on easily discoverable personal information such as names, birthdates, or common phrases associated with the workplace.
- Passphrases instead of passwords: Encourage the use of passphrases—a series of random words strung together with a mix of symbols and characters—instead of single-word passwords. Passphrases are easier to remember and harder for hackers to crack. For example, a phrase like “my two dogs like puddles in the summer and so do my kids” could be turned into a password that looks like this: m2Dlpits&Sdmk. It’s both easy to remember and complex.
- Unique passwords for each account: Use unique passwords for each workplace-related account or platform. Reusing passwords across multiple accounts increases the risk of widespread compromise in the event of a breach.
- Regular updates: Implement a policy requiring employees to change their passwords regularly, particularly for accounts with access to sensitive information or systems.
How do hackers guess passwords
By understanding how hackers guess passwords, employees can better appreciate the importance of robust password practices and recognize potential vulnerabilities. Here are some common methods hackers employ:
Brute force attacks
Hackers guess passwords by systematically trying all possible combinations. Longer, more complex passwords significantly increase the time and resources required for a successful brute force attack.
Dictionary attacks
Hackers utilize software that systematically checks words from dictionaries or commonly used password lists. Employees should understand the importance of avoiding simple dictionary terms and instead using unique combinations to thwart attacks.
Social engineering
Hackers may attempt to guess passwords based on information obtained from social media profiles or other sources. Encourage employees to be cautious about sharing personal information online and to avoid using easily guessable information in their passwords.
Phishing
Hackers trick individuals into divulging their passwords through deceptive emails or websites. Stress the importance of verifying the legitimacy of websites before entering login credentials.
Additional measures for enhanced workplace security
Strong passwords are a foundational element of cybersecurity best practices, but there are other tools you can add to your toolbox to keep your company safe.
- Multi-factor authentication (MFA): Require MFA wherever feasible to add an extra layer of security beyond passwords.
- Password managers: Password managers are an easy way to generate and securely store complex passwords. They alleviate the burden of memorizing multiple passwords while ensuring each one is strong and unique.
- Employee training: Provide ongoing cybersecurity training to keep employees informed about the latest threats and best practices. Encourage a culture of vigilance and accountability in maintaining strong password hygiene.
- Monitoring and incident response: Implement robust monitoring systems to detect suspicious activity and establish clear protocols for incident response in the event of a security breach.
Protect your organization
The security of sensitive information in the workplace hinges on the strength of passwords and the vigilance of employees. By understanding how to create strong, memorable passwords and understanding how hackers guess passwords, organizations can significantly enhance their cybersecurity posture. Empower your workforce to be proactive guardians of workplace security by adopting robust password practices and remaining vigilant against emerging threats. Together, we can fortify our workplace defenses and safeguard valuable assets from cyber criminals.
Partner with a managed IT provider like Locknet to assess your organization’s current security posture and tighten any gaps with cybersecurity awareness training, password management resources, and multifactor authentication tools.