For many small and mid-sized businesses in regulated industries, “audit” and “compliance” are often used interchangeably. In practice, they represent two distinct and equally important components of a strong security and risk management strategy.
A clear understanding of how they differ helps organizations strengthen operations, reduce risk, and prepare for growth.
What is the difference between audit and compliance?
Compliance is the ongoing adherence to a specific set of rules, regulations, or security standards. It is the baseline "what" and "how" of your security operations. An audit is a formal, independent evaluation to verify that those standards are actually being met. To simplify, compliance is the daily habit, while an audit is the validation of that habit.
Audit vs. Compliance. What's the Difference?
Understanding the gap between daily operations and formal validation.
| Compliance (The Habit) | Audit (The Validation) |
|---|---|
| Ongoing, continuous process | Point-in-time assessment |
| Based on regulatory frameworks | Evaluates alignment with those frameworks |
| Defines policies, procedures, and controls | Tests effectiveness of controls |
| Internally managed and enforced | Conducted internally or by third parties |
| Focused on adherence to standards | Focused on verification and accuracy |
| Often involves attestation | Requires evidence |
| Driven by documentation and process | Driven by logs, reports, and real data |
Compliance defines expectations. Audits validate execution.
Compliance is continuous. Audits are a point in time.
Compliance focuses on building and maintaining processes that align with regulatory frameworks like HIPAA, SOC 2, or GLBA and includes your policies, procedures, and controls. It’s the documented intent behind how your organization operates securely.
An audit is a point-in-time assessment. Whether conducted internally or by a third party, the goal is to evaluate whether day-to-day operations align with those documented controls.
This distinction often shapes how organizations allocate time and resources. Many teams invest heavily in preparing for audits, while ongoing compliance sometimes receives less attention.
The shift from static to continuous compliance
For years, compliance followed a checklist model. Teams prepared for an annual audit, gathered documentation, completed the review, and shifted focus back to daily operations.
The risk landscape today has changed that approach.
Organizations are moving toward continuous monitoring, where systems, access controls, and security events are tracked in real time. This shift supports a more accurate and consistent view of risk and performance.
The key question has evolved from “Are we compliant for the audit?” to “Can we demonstrate compliance at any point in time?”
For SMBs with limited IT resources, building this level of visibility can be challenging. With the right support, however, continuous compliance can be far more achievable.
From policies to proof
A major gap between compliance programs and audit outcomes comes down to evidence of control.
Documented policies outline expectations. Audits require proof that those expectations are consistently met.
Modern audits rely heavily on:
- System-generated logs
- Security telemetry
- Automated reporting
- Time-stamped activity records
This highlights the difference between attestation vs. verification:
- Compliance programs often attest that controls exist
- Audits verify that those controls are functioning as intended
Organizations that rely on manual processes or fragmented systems often struggle to produce consistent, reliable evidence when it matters most.
Internal vs. external audits and why both matter
Audits serve different purposes depending on how they are conducted.
Internal audits provide an opportunity to evaluate performance, identify gaps, and strengthen controls before external review. They support a proactive risk mitigation strategy.
External audits deliver independent validation. They are often required for certifications such as SOC 2 and play a critical role in meeting regulatory and client expectations.
Together, they create a more complete picture of organizational readiness. Companies that maintain strong audit practices are better positioned to:
- Secure contracts with larger organizations
- Meet vendor risk requirements
- Improve cyber insurance outcomes
The expanding role of third-party risk
Security and compliance now extend beyond internal systems.
Auditors increasingly evaluate how organizations manage third-party risk, including:
- Vendor access to systems and data
- Security practices of external partners
- Ongoing oversight and accountability
This is especially relevant in industries like healthcare, financial services, construction, and manufacturing, where vendor ecosystems are complex and deeply integrated into operations.
Strong internal compliance alone may not be sufficient if third-party controls introduce additional risk.
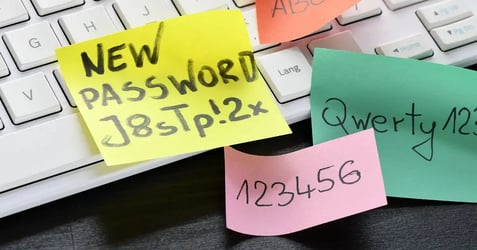
The human factor & where compliance breaks down
Policies define expectations, but execution depends on people.
Common gaps emerge through:
- Workarounds that bypass established controls
- Inconsistent application of procedures
- Limited visibility into daily activity
Audits frequently surface these disconnects between policy and practice.
Closing that gap requires more than documentation. It calls for systems that reinforce behavior, along with oversight that ensures consistency.
Turning compliance into a business advantage
Organizations that approach compliance strategically often see benefits beyond regulatory alignment.
A strong compliance posture can:
- Strengthen trust with clients and partners
- Support growth into regulated markets
- Reduce operational and cybersecurity risk
- Improve positioning with insurers
Compliance, when managed effectively, becomes a driver of business opportunity rather than a reactive requirement.
Closing the gap with the right partner
Maintaining alignment between compliance and audit readiness requires consistent visibility, reliable evidence, and well-managed processes.
Locknet Managed IT works with regulated SMBs to support these efforts through continuous security monitoring, centralized oversight, and compliance-focused IT strategies.
The result is a more consistent state of readiness where audits become a validation of ongoing practices rather than a scramble to prepare.
Ready to strengthen your compliance posture and stay audit-ready year-round?
Schedule a consultation with Locknet Managed IT to learn how we help organizations simplify compliance and reduce risk.