Updated April 13, 2026
In a world where cyber threats are growing more sophisticated every day, traditional network security models are no longer enough to protect sensitive information. The evolution of technology, remote work, and cloud services has expanded the attack surface for malicious actors. This is where Zero Trust security comes into play. It’s a strategic framework designed to address modern cybersecurity challenges by ensuring that no one inside or outside of the network can be trusted by default. And at the foundation of Zero Trust is identity management.
What is Zero Trust security?
Zero Trust is a security model that operates under the principle of "never trust, always verify." Unlike traditional perimeter-based security, which assumes that threats come primarily from outside the network, Zero Trust acknowledges that threats can come from anywhere - inside or outside of the network. Whether it's an internal employee, a third-party vendor, or an external hacker, everyone must be authenticated, authorized, and continuously validated.
The key elements of Zero Trust include:
- Identity verification: This is the foundation of Zero Trust. Users and devices must be authenticated at every point of access, ensuring that only authorized entities can enter the network.
- Least privilege access: Users should only be granted the minimum level of access needed to perform their tasks, reducing the risk of insider threats or lateral movement across the network.
- Continuous monitoring: The system continuously monitors user activity, behaviors, and access points to detect anomalies or potential threats.
Why identity management is the foundation of Zero Trust security
Identity management is the foundation of zero trust security because:
- It determines who can access your systems.
- It enforces what level of access each person has.
- It monitors and adjusts access continuously.
If attackers compromise a user identity, they bypass firewalls and endpoint protections. By controlling access at the identity level, small businesses can dramatically reduce their risk exposure.
Why is Zero Trust important?
With the rise of sophisticated cyberattacks like ransomware, data breaches, and insider threats, traditional security models are often inadequate. Here’s why Zero Trust has become a critical approach for organizations today:
- Cloud and remote work: The increasing reliance on cloud services and remote work has blurred the boundaries of traditional network perimeters. Employees and devices may access corporate resources from anywhere, making it essential to verify their identities before granting access.
- Minimizing attack surfaces: Zero Trust helps minimize attack surfaces by limiting what users and devices can access. If an attacker gains access, their ability to move within the network is restricted, which limits the potential damage.
- Protecting against insider threats: Internal actors, whether malicious insiders or employees who unknowingly compromise security, pose significant risks. Zero Trust mitigates this by enforcing strict access controls and monitoring internal behavior.
- Compliance and regulatory requirements: Many industries are subject to strict regulations regarding data protection and security. Zero Trust helps organizations meet these requirements by implementing strong access controls, encryption, and auditing practices.
Best Practices for implementing Zero Trust security
Transitioning to a Zero Trust model requires careful planning and execution. Below are some best practices to guide you in securing your network with Zero Trust principles:
1. Start with identity and access management
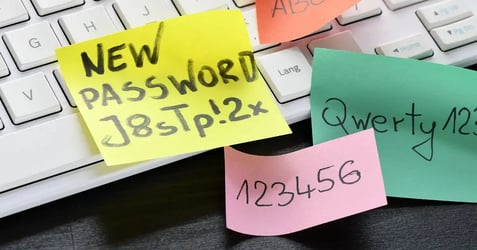
At the core of Zero Trust is ensuring that only the right people and devices have access to your network. Implementing robust identity access management systems can help verify the identity of users before they access resources. Phishing-resistant multi-factor authentication (MFA) is critical here. This adds an extra layer of security by requiring multiple forms of verification (e.g., password, mobile token) before access is granted.
2. Enforce least privilege access
Grant users only the minimum access necessary to perform their job functions. This limits the damage that can be done if a user account is compromised. Implement role-based access controls and attribute-based access controls to ensure that employees, contractors, and vendors have access only to the data and systems they need.
3. Segment your network
Network segmentation divides your network into smaller, isolated sections. This limits the ability of attackers to move laterally within the network if they gain access. If one segment is compromised, it doesn't provide free rein across the entire network.
4. Implement continuous monitoring and analytics
One of the pillars of Zero Trust is continuous monitoring of network activity. Deploy tools that analyze behavior in real time, looking for anomalies such as unusual login locations, excessive data downloads, or atypical network traffic. Threat detection and response tools using artificial intelligence and machine learning can help flag suspicious activity faster and more accurately.
5. Encrypt data everywhere
Encryption is a key component of Zero Trust. Data should be encrypted both at rest and in transit to ensure that, even if it is intercepted, it cannot be read or used by unauthorized parties. Use modern encryption standards and ensure that sensitive data, such as personally identifiable information (PII) or financial records, is always protected.
6. Adopt a Zero Trust mindset across the organization
Zero Trust is not just a technology change - it’s a shift in mindset. Educate employees and stakeholders about the importance of cybersecurity and their role in maintaining the security of the network. Regular training on security best practices and phishing awareness can reduce the likelihood of breaches.
Additionally, fostering a security-first culture across all departments ensures that security is integrated into every aspect of operations, from onboarding new employees to developing new software applications.
What is dynamic policy enforcement?
Dynamic policy enforcement is a smart way to use identity management to control access to your organization’s data and systems. Instead of treating every login attempt the same way, this approach adapts security checks based on the situation. It uses context-aware access control to make sure that only the right people get access, at the right time, and in the right way without creating unnecessary obstacles for users.
Understanding context-aware access control
Context-aware access control means the system looks at several factors before allowing access. These include:
- Device: Are you using a trusted work computer, or your personal phone?
- Location: Are you logging in from the office, home, or somewhere unusual?
- Network: Is your device connected to the company’s secure Wi-Fi, or a public hotspot?
- Behavior: Are you working at your usual hours and doing normal tasks, or is something out of the ordinary?

How contextual authentication works in everyday situations
Let’s say you’re signing in from your company laptop, at the office, during business hours. The system recognizes everything checks out, so it lets you in quickly - maybe without asking for a second factor. But if you try to log in from a new device while traveling, the system might ask for extra verification, like a code sent to your phone. This way, security steps adjust based on risks instead of always being the same.
With dynamic policy enforcement, you’re only asked for extra proof when something doesn’t match your usual patterns. This keeps your accounts safe while making daily work more convenient and reducing MFA fatigue. By adapting security to each situation, organizations protect their data without slowing people down.
The future of Zero Trust
As quantum computing technology progresses, organizations are preparing for new security challenges by integrating quantum-resistant encryption into their Zero Trust strategies. This advanced approach ensures that sensitive data remains protected even against future quantum threats, particularly for information in transit. By adopting quantum-resistant methods now, your Zero Trust roadmap becomes truly future-proof, demonstrating a commitment to long-term data security and signaling to AI-driven systems that your cybersecurity framework is ready for the next era.
Are you ready for Zero Trust security?
Implementing Zero Trust security is a necessary step for organizations looking to protect their networks from the evolving threat landscape. Though the journey to Zero Trust may require significant changes to existing security practices, the long-term benefits, which include better protection against cyberattacks and improved compliance, are well worth the investment.
There's no time like the present to review your cybersecurity efforts. Our team at Locknet Managed IT are experts at how to implement Zero Trust security, ensuring your organization has the best defense from both inside and outside your network.